The Nexus security team and community contributors published an updated PGP key verification guide in October 2025, responding to a notable increase in social engineering attempts where bad actors attempted to substitute their own PGP keys for legitimate vendor keys in forum posts and direct messages.
The attack works as follows: a fraudster identifies a popular, reputable vendor. They create a new PGP key with the same identity information (name, email). They then post "updated" key announcements in forums, direct message buyers claiming their key was "compromised," or edit their listing to display the fraudulent key. Buyers who encrypt their shipping address using the fraudulent key provide their address to the attacker, not the legitimate vendor.
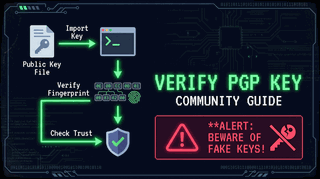
Verification Procedure
The guide emphasizes a three-step verification procedure: First, obtain the vendor's PGP key fingerprint from within the marketplace itself (not from forum posts). Second, verify that any "key update" announcement is signed by the old key — a legitimate vendor rotating keys will always sign the new key's fingerprint with the old private key. Third, cross-reference with independent sources such as the vendor's established Dread thread.
The guide also covers key expiry management, the importance of checking the key creation date (a brand-new key claimed to have been in use for a year is a major red flag), and the process for reporting suspected key fraud to the platform's trust team.
The complete guide is available on the platform's internal forums and has been integrated into the new user onboarding flow, ensuring all newly registered accounts receive the verification training before completing their first transaction.